The memset overflows the four bytes stack variable and modifies the canary value.
The 64bits canary 0x5429851ebaf95800 can't be predicted, but in specific situations is not re-generated and can be bruteforced or in other situations can be leaked from memory for example using a format string vulnerability or an arbitrary read wihout overflowing the stack.
If the canary doesn't match, the libc function __stack_chck_fail is called and terminates the prorgam with a SIGABORT which generates a coredump, in the case of archlinux managed by systemd and are stored on "/var/lib/systemd/coredump/"
❯❯❯ ./test
*** stack smashing detected ***:
fish: './test' terminated by signal SIGABRT (Abort)
[sudo] password for xxxx:
Decoding file core.test.1000.c611b7caa58a4fa3bcf403e6eac95bb0.1121.1574354610000000
core.test.1000.c611b : decoded 249856 bytes
❯❯❯ sudo gdb /home/xxxx/test core.test.1000.c611b7caa58a4fa3bcf403e6eac95bb0.1121.1574354610000000 -q
We specify the binary and the core file as a gdb parameters. We can see only one LWP (light weight process) or linux thread, so in this case is quicker to check. First of all lets see the back trace, because in this case the execution don't terminate in the segfaulted return.
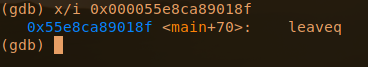
We can see on frame 5 the address were it would had returned to main if it wouldn't aborted.
Happy Idea: we can use this stack canary aborts to detect stack overflows. In Debian with prevous versions it will be exploitable depending on the compilation flags used.
And note that the canary is located as the last variable in the stack so the previous variables can be overwritten without problems.
Related links
- What Are Hacking Tools
- Pentest Tools Find Subdomains
- Hacker Tools 2019
- Github Hacking Tools
- Hack Tools Mac
- Pentest Tools Nmap
- Hacker Tools Free
- Tools For Hacker
- Tools 4 Hack
- Best Hacking Tools 2019
- Pentest Tools Open Source
- Hack Tools For Windows
- Hackers Toolbox
- Hack Tools Mac
- Usb Pentest Tools
- Hacker Tools Mac
- Termux Hacking Tools 2019
- Pentest Tools
- Hacks And Tools
- Hacking Tools Name
- Pentest Tools For Ubuntu
- Android Hack Tools Github
- Hack Tools For Pc
- How To Install Pentest Tools In Ubuntu
- Hacker Tools Free
- Pentest Tools Download
- Hacking Tools Windows 10
- Pentest Tools Tcp Port Scanner
- Hackrf Tools
- Hacking Tools For Mac
- Free Pentest Tools For Windows
- Hack Tools Mac
- Pentest Tools Github
- Hack Tools Online
- Hack Tools For Windows
- Pentest Tools Website Vulnerability
- Hack Tools For Ubuntu
- Hacker Tools Hardware
- New Hack Tools
- Pentest Tools Free
- Pentest Tools Kali Linux
- Hack Tools 2019
- Top Pentest Tools
- Ethical Hacker Tools
- Hacker Tools Free Download
- Hak5 Tools
- Pentest Tools Tcp Port Scanner
- Pentest Tools Port Scanner
- Pentest Tools Linux
- Pentest Tools For Android
- Hacking Tools Free Download
- Hacker Tools Online
- Install Pentest Tools Ubuntu
- Hacker Techniques Tools And Incident Handling
- Tools For Hacker
- Hacking Tools Name
- Hack Tools Mac
- Top Pentest Tools
- Hack Apps
- Pentest Tools Subdomain
- Nsa Hacker Tools
- Hacking Tools Windows 10
- Tools 4 Hack
- Hack And Tools
- Hack And Tools
- Pentest Tools Nmap
- Pentest Tools Url Fuzzer
- Pentest Tools List
- Hacking Tools Mac
- Hack And Tools
- Physical Pentest Tools
- Hacker Tools Software
- Pentest Tools Tcp Port Scanner
- Hacking Tools Hardware
- Pentest Tools Open Source
- Easy Hack Tools
- Hacker Hardware Tools
- Pentest Tools List
- Hacking Tools Software
- Hacker Tools For Windows
- Hacker Tools Online
- How To Hack
- Hacker Tools Free Download
- Hacker Tools Hardware
- Hacker Tools Apk Download
- Blackhat Hacker Tools
- Hacking Tools For Kali Linux
- Hack Apps
- Pentest Tools Website
- Hacker Tools 2019
- Pentest Tools Url Fuzzer
- What Are Hacking Tools
- Growth Hacker Tools
- Hack Rom Tools
- Best Hacking Tools 2020
- Pentest Tools Windows
- Hacking Tools For Beginners
- Hacking Tools Online
- Bluetooth Hacking Tools Kali
- What Is Hacking Tools
- Pentest Tools Bluekeep
- Hacking Tools For Games
- Hacking Tools Software
- Top Pentest Tools
- Android Hack Tools Github
- Hacking Tools For Mac
- Hacker Tool Kit
- Hacking Tools Hardware
- Pentest Tools Nmap
- Hack Tool Apk No Root
- Hack Tools
- Pentest Tools Open Source
- Hacking Tools Kit
- World No 1 Hacker Software
- Pentest Tools For Mac
- Hacking Tools Windows
- Pentest Tools Apk
- Hacker Tools Windows
- What Is Hacking Tools
- How To Make Hacking Tools
- Hacking Tools For Windows
- Hack Tools
- Hacking Tools For Windows Free Download
- Hacking Tools For Beginners
- Pentest Tools Tcp Port Scanner
- Wifi Hacker Tools For Windows
- Hacker Techniques Tools And Incident Handling
- Pentest Reporting Tools
- Hacking Tools Download
- Hackrf Tools
- Hacking Tools Software
- Pentest Tools Download
- Growth Hacker Tools
- Kik Hack Tools
- Hacker Search Tools
- Pentest Tools
- Hacker Tools Free Download
- Hacker Tools For Windows
- Hacker Tools Online
- Usb Pentest Tools
- Hack App
- How To Hack
- Hacking Tools Online
- Hacking App
- Hacker Hardware Tools
- New Hack Tools
- Pentest Tools Website Vulnerability
- Github Hacking Tools
- Hacker Tools List
- Kik Hack Tools
- Hacking Tools Download
- Install Pentest Tools Ubuntu
- What Are Hacking Tools
- Nsa Hacker Tools
- Nsa Hack Tools Download
- Hacking Tools Online
- Hacker Tools Free Download
- Hacking Tools For Beginners
- Pentest Reporting Tools
- Pentest Tools Apk
- Hack And Tools
- Hack Tools Pc



No hay comentarios:
Publicar un comentario